The Mevade adware was recently associated to a sudden surge of in the number of Tor users during the last month. As it turned out, Mevade downloaded a Tor component on infected computers, potentially as a support mechanism for its command and control communications.
“In addition to the Mevade malware itself, we saw that ADW_BPROTECT had also been downloaded onto affected systems,” blogged Roddell Santos, threats analyst at Trend Micro. “This is expected for Mevade, as we noted earlier that it is linked to cybercriminals responsible for the distribution of adware. This downloading of adware is consistent with our findings that the Mevade botnet is possibly monetized via installing adware and toolbars.”
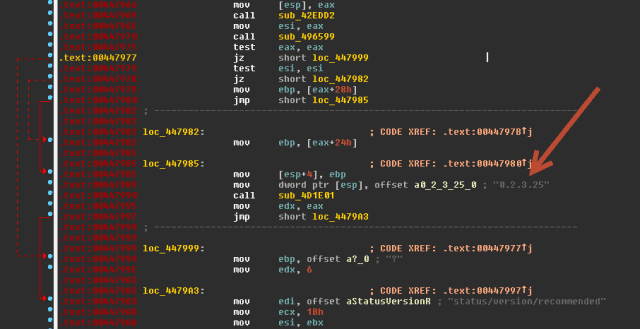
Trend Micro states, a batch of Mevade samples the company’s researchers analyzed were downloaded by a malicious file named FlashPlayerUpdateService.exe (detected by Trend Micro as TROJ_DLOADE.FBV) – which is the same file name as the legitimate file. However, the real updater file is signed by Adobe Systems, whereas the malicious one is not. In addition, the version numbers are different.
“The backdoor communicates to its C&C server via HTTP to receive commands, which include updating a copy of itself and connecting to a specific location using SSH to secure its communication,” Santos blogged.
“As for TROJ_DLOADE.FBV, we’ve found that the URLs it uses to access its C&C servers has the following pattern:
- http://{malicious domain}/updater/{32 random hexadecimal characters}/{1 digit number}”
The IP addresses that host these C&C servers are located in Russia, though TROJ_DLOADE.FBV was found in multiple countries, with Japan and the United States being hit the hardest.
As for Mevade, most of the victims (95 percent) are located in the United States.
Santos recommended that users observe best practices and avoid visiting suspicious sites and downloading files. In addition, users should keep their software up-to-date.
Cross-posted from www.securityweek.com