Researchers have identified a banking trojan, named ‘Tinba’ or ‘Tiny Banker,’ has been targeting innocent customers of at least 26 different banking institutions globally.
In accordance with security corporation Avast, the malware has resurfaced and broadened its targets after its first discovery nearly two years ago when it infected thousands of computer systems in Turkey.
This season, the malware was seen deceiving Czech customers into supplying their financial details, but researchers say it now gone international.
A list of recently targeted banking institutions consists of many major US-based banks, including Bank of America, US Bank, Chase and Wells Fargo.
Avast security experts David Fiser and Jaromir Horejsi clarify within a article how the Tiny Banker malware effectively obtains personal and financial information from customers trying to access their banking account online.
1. The user visits a website infected with the Rig Exploit kit (Flash or Silverlight exploit).
2. If the user’s system is vulnerable, the exploit executes a malicious code that downloads and executes the malware payload, Tinba Trojan.
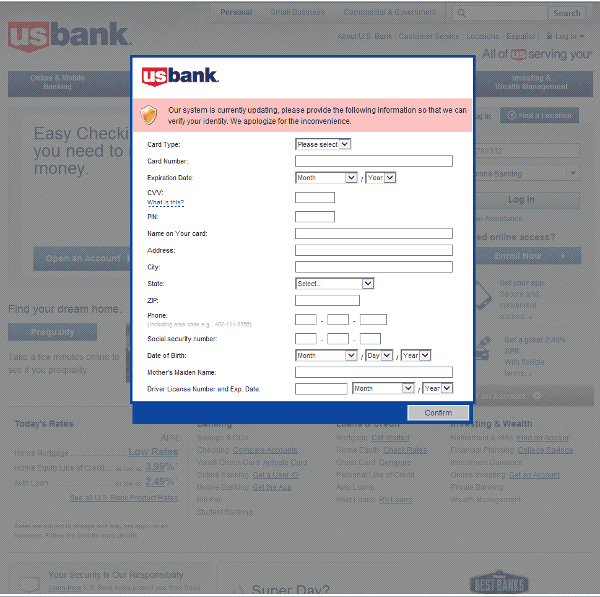
3. When the computer is infected and the user tries to log in to one of the targeted banks, webinjects come into effect and the victim is asked to fill out a form with his/her personal data.
4. If he/she confirms the form, the data is sent to the attackers.
This page is injected with code from the Malware to extra field including credit card number, CVV and other personal data.
Regardless of its 20k code base, experts state the trojan’s capabilities are potent. The malware continues to be seen distributed by the Rig exploit kit, with changes likely because of its leaked source code back in July, which can be downloaded here.