About 10,000 Australians have already been targeted in a Cryptolocker ransomware campaign that persuades individuals with an email that seems to come from local energy company AGL, as reported by the Sydney Morning Herald.
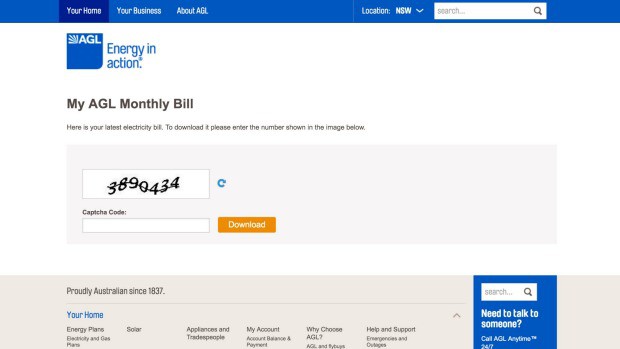
A bogus bill seems to be coming from the energy provider, but when a user clicks on a link to download their bill, a .zip file is downloaded instead. The malware then freezes the device, at which a payment of $640 is required to remove the malware.

As the emails are intended for users at their office, another serious risk is the attackers will obtain access to corporate emails which may then be used to spread the scam further.
Once the malware is delivered, the only option would be to restore from a backup or to wipe the computer’s hard drive and begin from scratch, said Raymond Schippers, a senior specialist at Check Point, which investigated the ransomware.
He said an analysis by Check Point found at least 10,000 people had actually gone to the end of the download process, and were “very likely to have been infected”, while “many more” could have been affected.
The website used URLs such as “checkyourbills.com” or “electricitybill.com” and would look legitimate to “most users”, he said.
There are a couple ways customers can tell the email is fake.
When a receiver tries to open it within their phone or on a Mac computer, it gives you an error message and claims to use a Windows computer, also, the .zip file type is shady.
“Realistically, if you open it on your iPhone and it says ‘this doesn’t work on an iPhone’, it probably isn’t a real website,” Mr Schippers said. “All the websites from all Australian utilities work on phones these days.
“The .zip file is another indication that it’s not usually a bill either. They usually don’t send bills as .zip files, they’ll send them as .pdf or something similar.”