Based on Check Point’s analysis of the Nuclear Exploit kit (EK), the coders are estimated to earning over $100,000 every month.
Renting out exploit kits is nothing new, for example the Blackhole EK was selling all over underground forums using other users as re-sellers. But Nuclear is climbing to new heights, existing on the black market since early 2010.
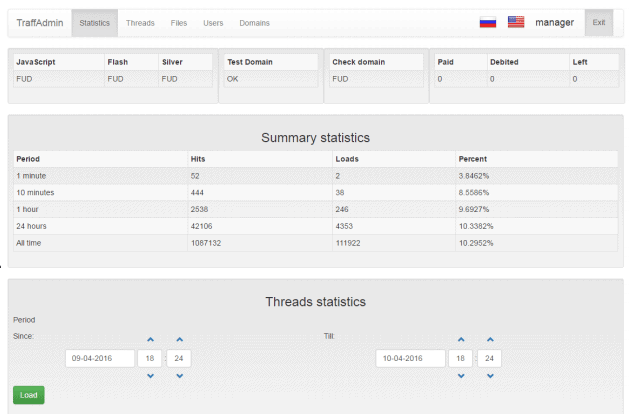
Similar to its rivals, the Nuclear EK is usually rented to attackers for a restricted duration and the attackers are then given access the EK’s control panel. Based on the Check Point’s analysis, this panel is operating on a nginx/1.8.0 server using a non-trivial port so it stays hidden from web crawlers. The control panels are all connected to one master server. This server provides the Flash, JavaScript and VBScript exploits as well as it keeping them undetected.

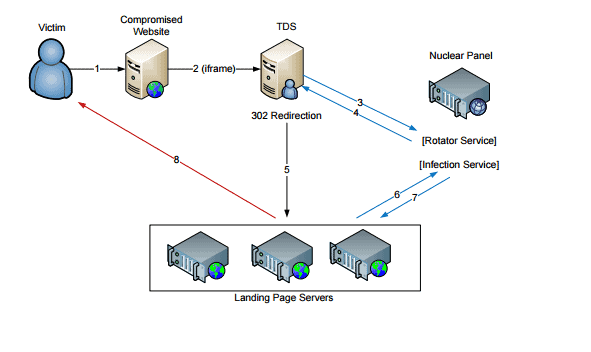
The traffic, malware and traffic distribution service (TDS) are the up to the buyer, below you can view the path a unsuspecting victim will follow.
Check Point’s report states that they’ve discovered 15 active control panels for Nuclear which are rented for a couple thousand dollars per month. It’s estimated that the creators of the Nuclear EK are earning nearly 100K USD each month.
Current infection rates of the Nuclear Exploit Kit:
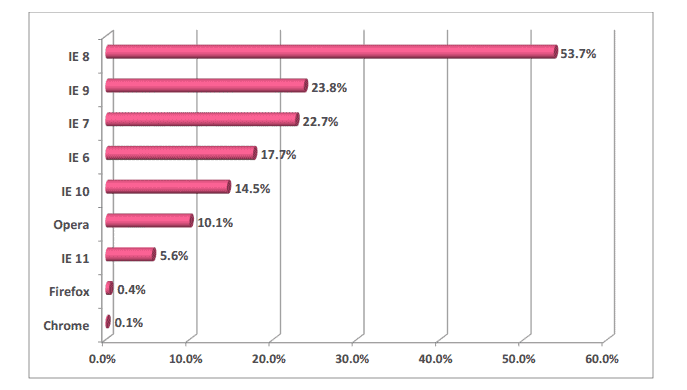
Check Point states that 1,846,678 machines were attacked and 184,568 machines have been successfully exploited, which is close to a 10% infection rate. In the graph below you are able to see the infection rate per browser with Internet Explorer 8 leading the chart.