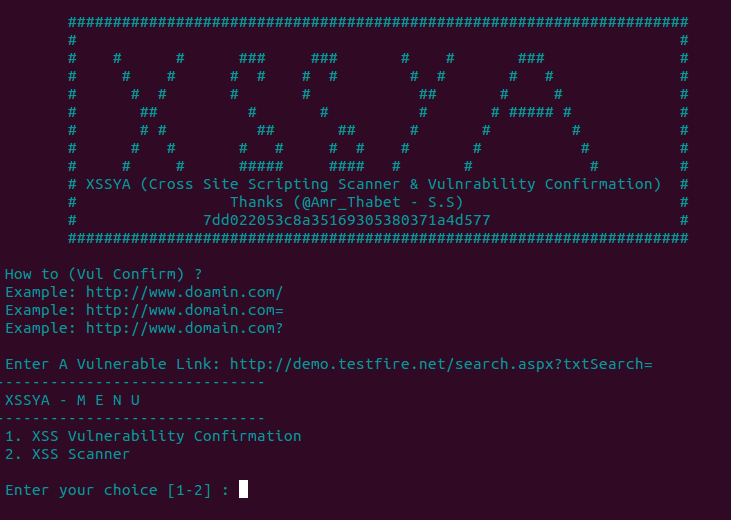
When a web application penetration tester begins scanning a website using a vulnerability scanner, it can give them a false positive vulnerability. This can happen because many scanners use a method of request and response where the scanner executes a payload and if the web page’s response is “200” then it’s vulnerable. This in fact is not enough to confirm the vulnerability and in this case, the penetration tester needs to confirm it manually. With XSSYA, you can confirm the XSS -Cross-Site Scripting Vulnerability without using a browser.
XSSYA – How It Works
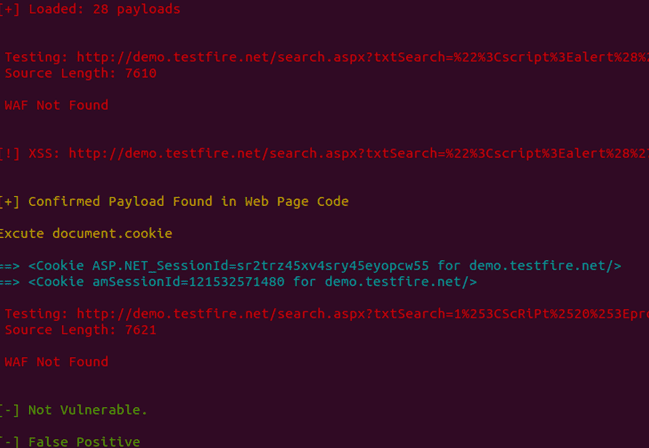
XSSYA works by executing the payload encoded to bypass any web application firewalls which is the first request and response. If there’s a response of “200”, it turns to Method 2 which searches the payload decoded in web page HTML code. If this is confirmed is will begin executing the last step which is “document.cookie” to get the cookie.
Demo video:
XSSYA Features
- Support HTTPS
- After confirmation execute payload to get cookies
- Can be run in Windows & Linux
- Identify 3 types of WAF (Mod_Security – WebKnight – F5 BIG IP)
- XSSYA contains a library of encoded payloads to bypass WAF (Web Application Firewall)
- Supports saving the web HTML Code before executing the payload by viewing the Web HTML Code on a screen or terminal