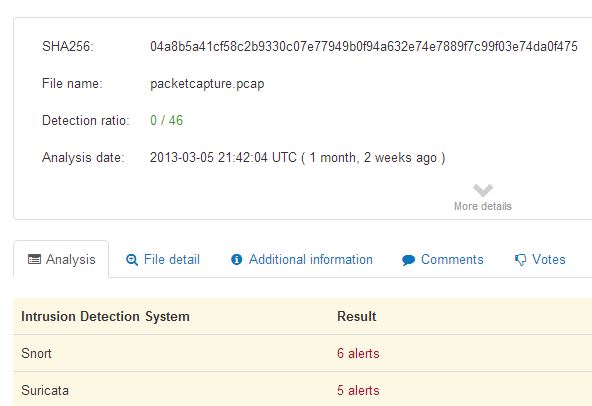
The popular VirusTotal service, which was recently bought out by Google and can run more than 20 anti-virus scanners over a sample in one pass, can now also look for traces of malware infections in captured network traffic.
To perform a check, users upload network packets that are captured in the common PCAP format instead of sending VirusTotal the more traditional suspicious EXE, PDF or HTML file.
Such network traffic dumps can be created with sniffers like Wireshark or tcpdump. VirusTotal will extract all transmitted files and present them to the familiar virus scanners; registered users will also receive copies of the extracted files. The scan service also looks at the network traffic data with the Snort and Suricata intrusion detection systems. These services can, for instance, detect the communication between a botnet client and its command & control server, as well as other typical attack patterns.
The analysis that VirusTotal executes can, in essence, also be performed by manually running each scanner one by one. The new analysis feature isn’t aimed at amateur users – who will likely not make much of messages such as “NETBIOS SMB-DS DCERPC NetrpPathCanonicalize request (possible MS06-040)” – but for administrators and security specialists, it provides a very quick way of extracting useful information.
Originally posted: www.h-online.com