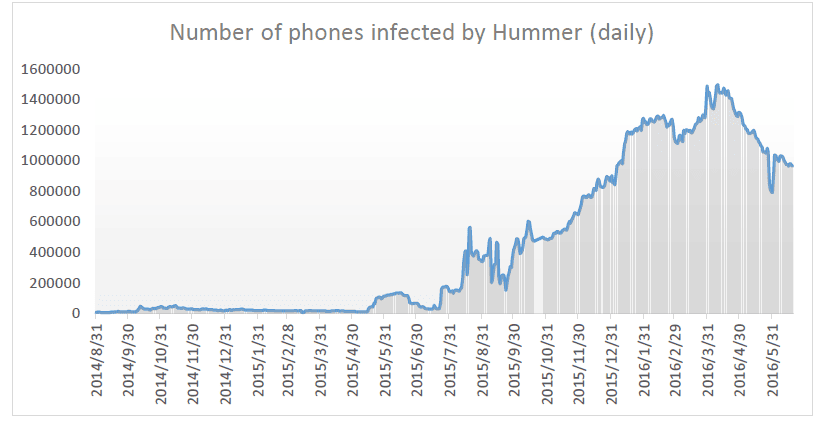
A new Trojan, named Hummer, has been discovered infecting Android phones. The malware creators are earning an estimated $3,500,000 a week or $500,000 a day say researchers at Cheetah Mobile Security Lab in a blog post.
In an alert given Wednesday, analysts claimed that at its peak, Hummer infected about 1.4 million Androids daily with 63,000 infections occurring everyday in Asia. This trojan variant, considered to be among the most prominent ever, may be linked somehow to “the underground industry chain in China.”
If Hummer’s makers generate 50 cents every time the virus is installed on a smartphone app, they can expect to easily earn half a million dollars.
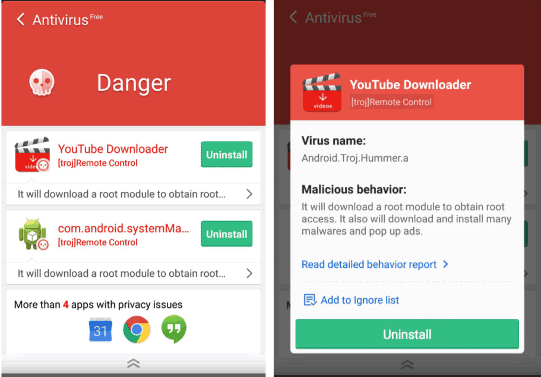
When a phone is infected, Hummer auto-roots it to achieve admin privileges, which makes it hard if not impossible for conventional anti-virus tools to eliminate it. All members of the trojan family are integrated with a root module while the Hummer variant includes up to 18 different root techniques, the researchers stated.
Beginning in early 2016, the team behind the Hummer malware began to use 12 domain names, a number of them associated with an email in mainland China, to upgrade Hummer and release promotion orders Cheatah Mobile stated.
“The researchers believe that this trojan family originated from the underground internet industry chain in China, based on the trojan codes that have been uploaded to an open-source platform by a careless member of the criminal group behind the trojan family,” as stated by the blog, which mentioned that the volume of phones being infected with Hummer is far beyond any other mobile phone malware.
It also might be the most bothersome. “This trojan continually pops up ads on victims’ phones, which is extremely annoying. It also pushes mobile phone games and silently installs porn applications in the background,” “Unwanted apps appear on these devices, and they’re reinstalled shortly after users uninstall them.”
In a experiment performed by Cheetah, “the trojan accessed the network over 10,000 times and downloaded over 200 APKs, consuming 2 GB of network traffic,” tasks which the experts said was “astonishing.”
Removing the Hummer Malware
Cheetah has updated their Trojan Killer app to effectively remove the Hummer malware, and it’s available on the Google Play store for all android devices, here.