A botnet consisting exclusively of internet-designed closed circuit TV appliances launched queries of HTTP requests to hit a small jewelry store offline for several days.
Experts who discovered the botnet stated they weren’t shocked that IoT systems were utilized to execute a distributed denial of service attack but were caught by surprise that it managed to sustain itself for so long and use over 25,000 CCTV devices to do so.
Experts at Sucuri first discovered the store, one of their customers, was being hit with a layer 7 HTTP flood attack that produced 35,000 HTTP requests a second. The analysts saw an uptick in requests coming from a following attack, which peaked at 50,000 requests a second shortly after, and encouraged Sucuri to look further into the attacks.
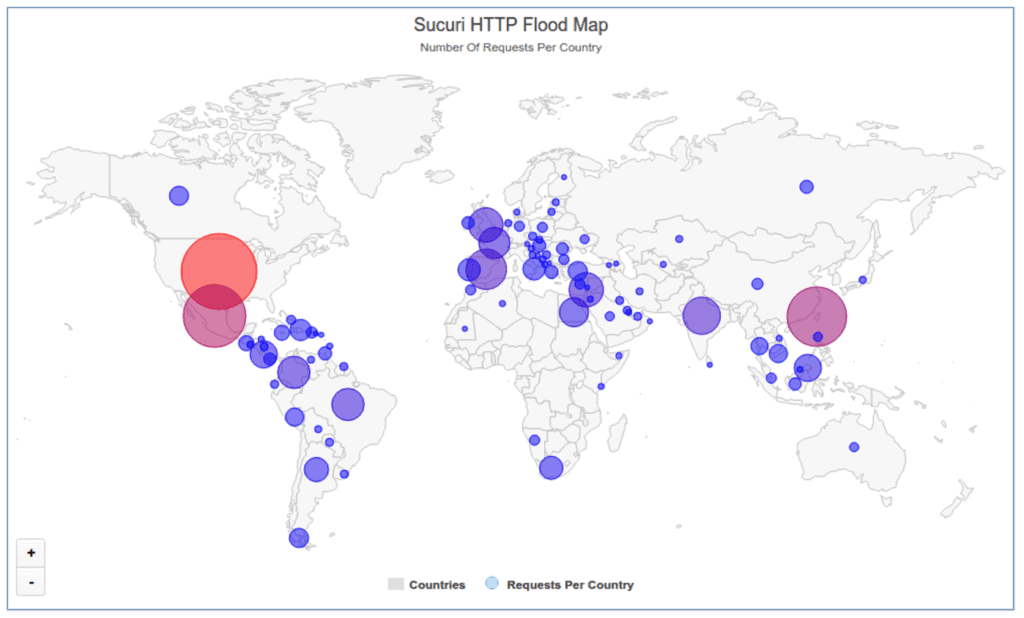
It was afterwards they discovered 25,513 different IP addresses, the majority of them located in Taiwan. The botnet was producing a DDoS attack over just a couple of hours, reported Daniel Cid, Founder and CTO of Sucuri, who wrote a blog post about the botnet on Monday.
The remainder of the IP addresses were mainly spread across Indonesia, Mexico, Malaysia, and Israel, but after analysts broke down its geographic dispersal, they noticed the botnet actually relied upon IP addresses from 100+ countries worldwide. As experts proceeded to look into it they found the majority of the botnet’s traffic was originating from devices running Cross Web Server, a kind of software that is used in several types of CCTV DVRs.
The majority of the devices, 46 percent, are H.264 Network Digital Video Recorders. Other systems include CCTV boxes produced by an Israeli company, Provision-ISR, a device manufacturer available in Home Depot and Costco stores, Q-See, and a manufacturer located in Vietnam, Questek, Sucuri reports.
Cid claimed Monday that all the devices are powered by BusyBox, a software that offers Unix tools in a single executable file and can be run in Linux, Android, and FreeBSD.
It’s not likely the CCTV systems will get patched in the near future. If they are, attackers will just move onto the next one, Cid claims.