An Internet Explorer exploit utilized in high-profile watering hole attacks has been included with the widely used Nuclear exploit pack.
The exploit affects unpatched versions of Internet Explorer and was applied in November to infect users interested in national and international security policy via an unnamed US policy website. The payload was loaded straight into memory without the need of first writing to disk, which FireEye researchers who identified the attack said had been a trademark of sophisticated attackers, and left no clues to uncover infected endpoints.
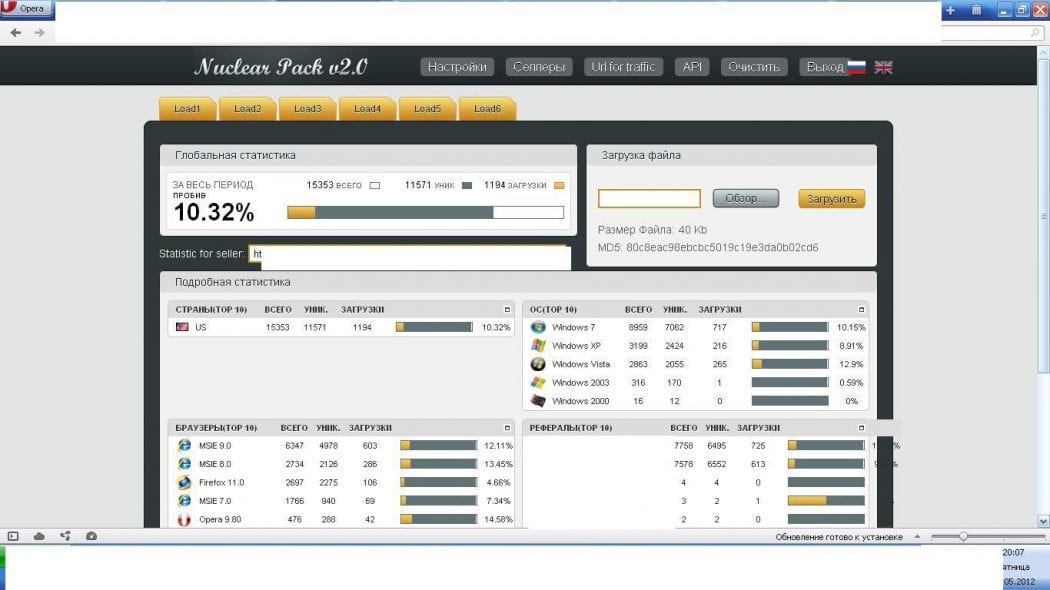
An independent security researcher Kafeine found the exploit included in the Nuclear Pack available on underground forums.
Nuclear is among the most favored exploit kits on the market now, providing a packed framework of payloads and client-side exploits for making attacks easier and much more efficient.
Microsoft said the exploit is a product of two distinct vulnerabilities; a remote code execution vulnerability (CVE-2013-3918) within the InformationCardSigninHelper ActiveX component employed by Internet Explorer, with a information disclosure vulnerability to enhance the reliability of the hack.
It affects Internet Explorer versions 7 and 8 on Windows XP and 7, but was foiled by Microsoft’s Enhanced Mitigation Experience Toolkit add-on.
With the fall of the Blackhole exploit kit, many malware authors are fighting for the top position. Kaspersky researcher Kurt Baumgartner mentioned that a successor to BlackHole could be “years away“, but researchers at Kahu Security recently stated the outdated RedKit exploit kit was appearing to be resurrected in the wake of the fall of BlackHole.