On November 11, Microsoft published a blog post about the latest zero-day (CVE-2013-3918) impacting an Internet Explorer Active X Control, that had been publicly disclosed on November 8. The blog claims that this vulnerability is scheduled to be addressed in “Bulletin 3”, which will be released as MS13-090 today via Windows Update at approximately 10:00AM PDT.
“The exploit leverages a new information leakage vulnerability and an IE out-of-bounds memory access vulnerability to achieve code execution,” was explained in the blog post Friday.
After having identified the latest IE zero-day exploit being actively used in the wild, FireEye researchers have revealed that the watering hole attack is more than likely mounted by the same Chinese hacker group that attacked Bit9, Hidden Lynx.
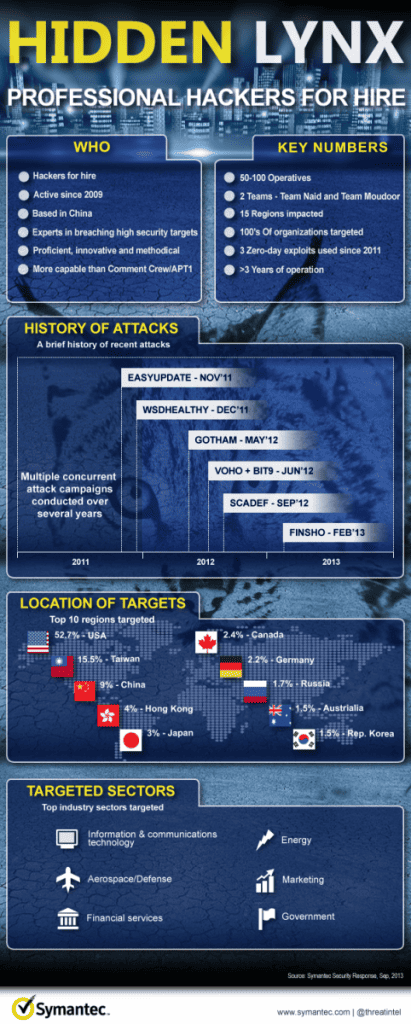
You can view an infographic describing Hidden Lynx, made by Symantec.
“The memory access vulnerability is designed to work on Windows XP with IE 7 and 8, and on Windows 7,” they shared. “The exploit targets the English version of Internet Explorer, but we believe the exploit can be easily changed to leverage other languages. Based on our analysis, this vulnerability affects IE 7, 8, 9, and 10.”
The breached site that hosts exploit is located in america and a well-known stop for readers thinking about national and global security, the researchers claim, but they didn’t identify the affected site. Visitors whose internet browser was susceptible to this particular exploit had a Remote Access Trojan (RAT) dropped onto their systems.
The RAT that was dropped was not added to startup, so a simple reboot removes it from the system. Experts assume that the attackers are either sure that the victims will go to the same site very often and get infected yet again, or that a brief time-frame will likely be sufficient for the attackers to gain access to other systems within the organization within the network.