Kaspersky Lab has reported the first sighting of Android malware that piggybacks on separate mobile botnets and uses the resources of other malware once it’s installed.
“For the first time malware is being distributed using botnets that were created using completely different mobile malware,” said Kaspersky Lab expert Roman Unuchek in a report.
The perpetrator is trojan called Obad.a, which the company has already marked as the most advanced piece of mobile malware they’ve spotted. It comes in 12 variants thus far, and commonly spreads via SMS, hacked apps websites or in 3rd party app stores.
Now it seems the Obad boys have teamed up with the makers of malware called Opfake.a, which applies a separate formula of multiplication by exploiting a flaw in Google Cloud Messaging. GCM was configured to ping out updates and fix phone settings remotely, and allows for the sending of 4KB messages to anyone using a specific application.
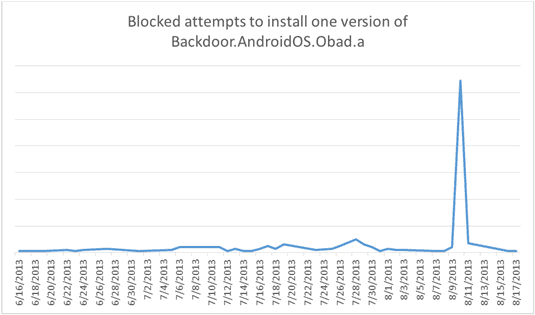
“These peaks are the result of using third-party botnet resources – mobile devices infected with other malware,” said Unuchek. “That means that the owners of Backdoor.AndroidOS.Obad.a not only command their own software to spread itself, they also take advantage of Trojans operated by other cybercriminals.”







