 After the release of Securelist’s whitepaper on the Gauss cyber-attack, they’ve been asked if there’s a painless way for users to determine if their system is infected. Normally the most dependable way is to download and install an Antivirus or use the free Kaspersky Virus Removal Tool.
After the release of Securelist’s whitepaper on the Gauss cyber-attack, they’ve been asked if there’s a painless way for users to determine if their system is infected. Normally the most dependable way is to download and install an Antivirus or use the free Kaspersky Virus Removal Tool.
GAUSS has been detected on 2,500 computers, mostly in Lebanon according to Kaspersky. The code tries to acquire logins for email and instant messaging accounts, social networks and also bank accounting information.
The report says that the Bank of Beirut, Byblos Bank, Blom Bank and Credit Libanais have been targeted along with the online payment system Paypal.
Costin Raiu, Kaspersky’s director of global research and analysis said in an interview “We have never seen any malware target such a specific range of banks. Generally, cybercriminals target as many banks as possible to maximize financial profit, but this is a very focused cyberespionage campaign targeting certain users of online banking systems.”
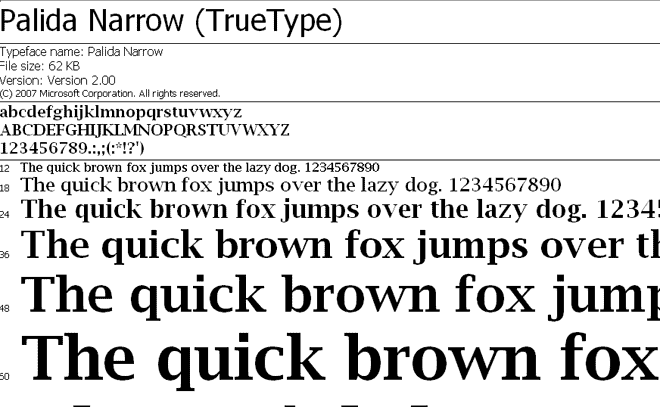
The thought of checking the system utilizing a webpage comes from the wellknown Hungarian research lab, known as CrySyS. They’ve also presented a web-based formula to check your system for Palida Narrow. Their test webpage is currently available here: http://gauss.crysys.hu.
Securelist has given the users some examples of the iframe window which holds the javascript code check to verify whether you have the mysterious Palida Narrow font installed.
This font was applied during the Gauss cyber-attack. Although many sill don’t presently understand precisely why the aggressors have installed this font, it could serve as an indicator of Gauss activity on your system.








#Gauss – Believed to be #State #Funded http://t.co/gPGXpmxp #Malware #Infosec
#Gauss – Believed to be State Funded – @Zer0Security http://t.co/cz2YuZGm