A security researcher that goes by the Twitter name @WilyXem, a pen-tester from Spain. Earlier we posted a false claim, which was just a SQL error, not necessarily a SQL injection vulnerability.
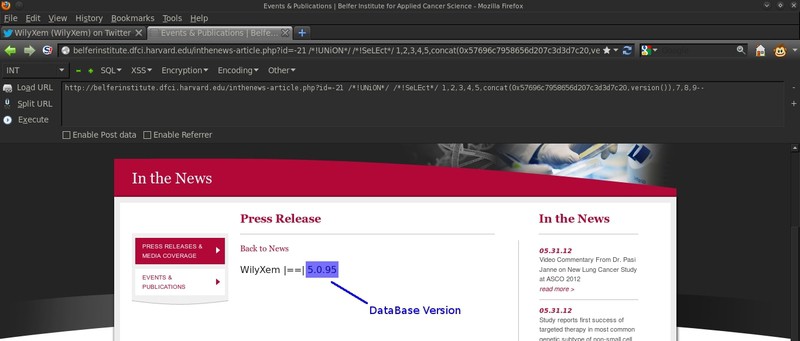
@WilyXem notified us and then found a real vulnerability within one of Harvard’s sub domain.
You can view the Tweet announcing the exploit below:
http://t.co/YPktfuRQ – Subdomain SQL Injected by WilyXem. http://t.co/VFQipGT8 @Zer0Security @ehackingnews @Softpedia @securityninja
— WilyXem (@WilyXem) January 30, 2013







lol that’s a sub-sub domain, c0rrupt.net has like 10x better harvard and other .edu/.gov sqli’s released for all of their members.
c0rrupt.net What you found in Harvard.edu Subdomain was an File Include error no SQL Vulnerability, so shut a fuck up. Your members are skiddies.
You obviously have seen none of our released vulnerabilities bitchboy :)
“bitchboy” ? If you think your team is great, why did you post the fucking file include error in the subdomain of harvard? You know, with that post “http://zerosecurity.org/security/harvard-edu-subdomain-vulnerable-to-sql-injection/” which was deleted, because was a bullshit, a fake vulnerability. And you guys, your called “Researchers and Hackers”? With the tweet of “Harvard subdomain injection” you’ve shamed.