Hackers have altered DNS records of websites hosted by Go Daddy, with the intention of infecting visitors with ransomware. The attackers are adding subdomains to the DNS records, pointing to a malevolent IP under the attacker’s command, allowing victims to trust they’re going to the correct website, and for the pages to void several security protection mechanisms.
This attack comes two months after an alleged attack on the Go Daddy network.
The server is being pointed to the Cool Exploit pack, which is scripts hosted on a web host/server, usually compromised, that uses a number of different vulnerabilities, in an effort to infect the visitors computer.
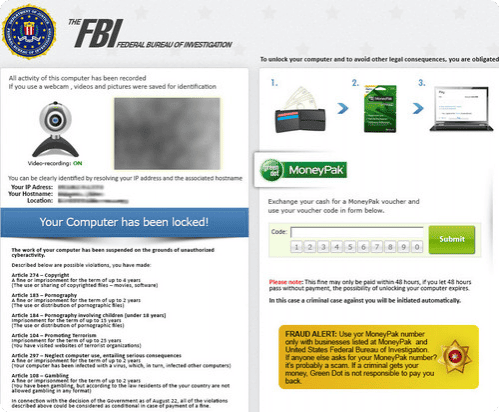
When infected, users are presented with a payment page that displays region-specific lock screen that causes the computer to appear as if it’s been locked down by local law enforcement. The page uses a webcam that claims to record the user for identification purposes as well as a list of potential offenses that the user is said to have committed, and that if a fine is not paid within a certain timeframe, the computer would be locked down completely.