Researchers at Kaspersky Labs have discovered a new attack by Advanced persistent threat (APT) actor LuoYu utilizing the known malware WinDealer.
WinDealer has the unique ability to perform attacks via a man-on-the-side attack. “This groundbreaking development allows the actor to modify network traffic in transit to insert malicious payloads,” said the Kaspersky researchers in a new report. “Such attacks are especially dangerous and devastating because they do not require any interaction with the target to lead to a successful infection,” they added.
LuoYu has been active since 2008 and mainly targets foreign diplomatic organizations established in China, academic communities, as well as logistics, defense, and financial companies.
Usage of WinDealer was first discovered by Taiwanese security firm Team T5 at the Japan Security Analyst Conference (SAC) in January of last year. Attack campaigns have been ongoing utilizing this specific malware to target Japanese entities with infections seen in India, Russia, Germany, Austria, and the United States.
The group has also deployed other malware including Plugx and its successor Shadowpad, which many other Chinese APT groups have used to achieve their objectives. The threat actor is also known to target Android, Linux, and Mac OS operating systems.
WinDealer appears to have been spread via websites that function as watering holes and by means of backdoored instant messaging and video hosting services like Tencent QQ and Youku.
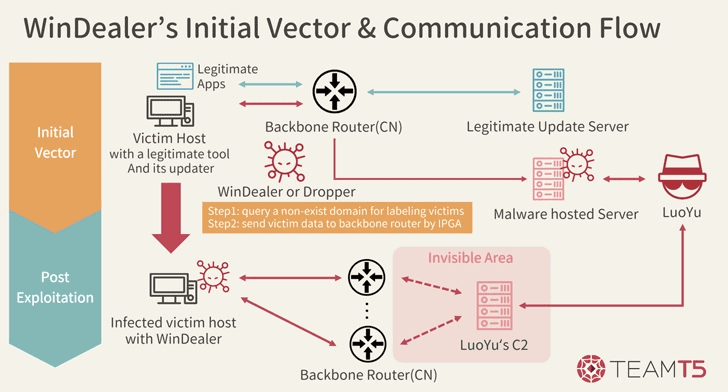
Recently, WinDealer has utilized a new method of distribution which includes making use of the automatic update features that most legitimate programs have and updates to a backdoored version. But this method has only been seen on rare occasions.
Once the target is infected, WinDealer will assist the attacker in searching for and pulling large amounts of data from the compromised Windows hard drive. WinDealer will also deploy various methods to maintain persistence in the system, meaning it’s harder to remove. The malware also has the ability to manipulate files, scan for other devices on the network, and is able to run commands given by the attackers.
To maintain the anonymity of WinDealer’s infrastructure and to delay or evade detection, the malware authors are not using the common hard-coded command-and-control (C2) server IP or DNS within the malware. WinDealer connects to a random ChinaNet (AS4134) IP address pool from the Xizang and Guizhou provinces that contains 48,000 IP addresses according to the researchers at Kaspersky.
It is unlikely that LuoYu owns all 48,000 IP addresses, but Kaspersky believes it to be a network of compromised routers “on the route to (or inside) AS4134,” the use of ISP-level law enforcement tools, or “signals intelligence methods unknown to the general public.”
“Man-on-the-side-attacks are extremely destructive, as the only condition needed to attack a device is for it to be connected to the internet. Even if the attack fails the first time, attackers can repeat the process over and over again until they succeed,” explained Kaspersky researcher Suguru Ishimaru.
“No matter how the attack has been carried out, the only way for potential victims to defend themselves is to remain extremely vigilant and have robust security procedures, such as regular antivirus scans, analysis of outbound network traffic, and extensive logging to detect anomalies.”
“LuoYu is an extremely sophisticated threat actor able to leverage functionality available only to the most mature attackers. We can only speculate as to how they were able to develop such capabilities,” Suguru Ishimaru stated.







