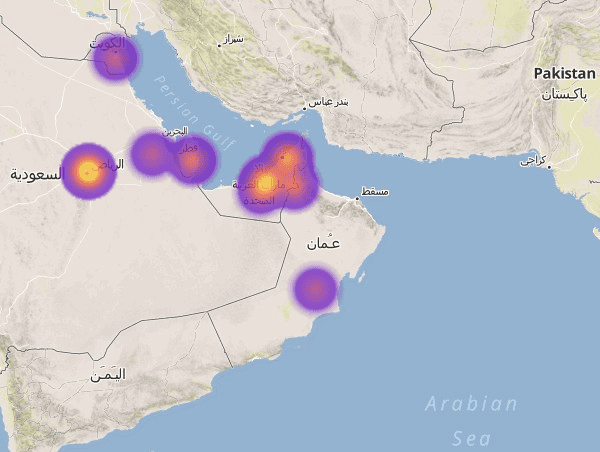
IntelCrawler, a cyber intelligence firm identified a sizable fraud campaign targeting large Islamic financial institutions. The attackers used a substantial mobile botnet with more than 27,000 intercepted SMS messages discovered between April 2013 and Feb 2014, which puts many smartphone banking customers at an increased risk.
The experts discovered the malware which often infected the cellular devices of banking customers to affect two-factor authentication components integrated through the banking institutions. The malicious code, as with any similar banking Trojan, has the ability to intercept one-time passwords (OTP) utilized to verify user’s transactions and are sent to the bot’s command and control servers which have implemented several kinds of encrypted notifications, which include alerts through Jabber.
The attackers cloned many legitimate mobile banking apps used in the Middle East banking institutions.
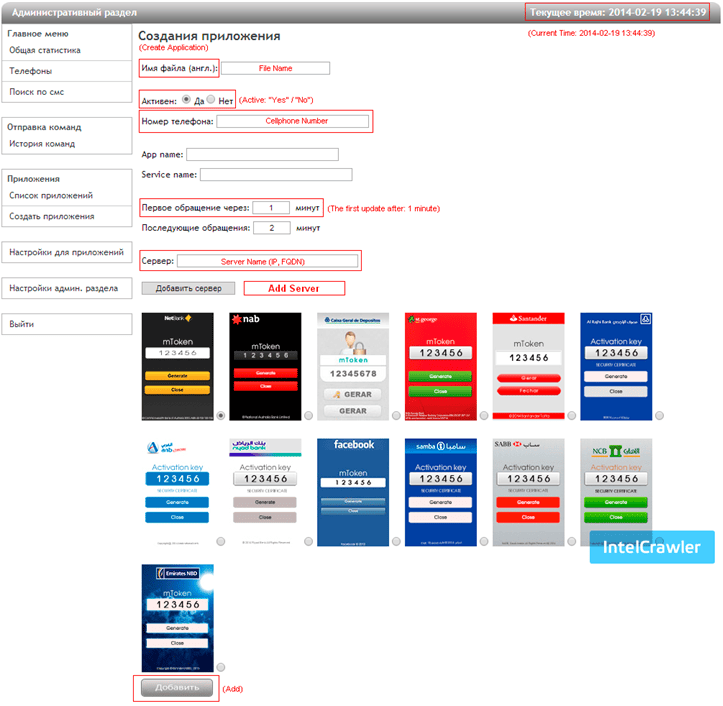
IntelCrawler has dubbed the banking trojan “mtoken-user7903.com”, the domain employed for the attacks was made on 5th February combined with a number of very similar domains such as “mtoken-user1034.com”, “mtoken-user3110.com”, “mtoken-user4901.com”, “mtoken-user7230.com”.
The Telecommunications Regulatory Authority (TRA) verified the fact that the amount of attacks is growing rapidly within the last three years, from 8,400 in 2010 up to 530,000 within the first quarter. TRA also disclosed to have detected over half a million cyber attacks on UAE computer users in the first three months of 2013.