Now Reuters is reporting that cyber intelligence firm IntelCrawler has uncovered proof linking no less than six ongoing schemes at U.S. merchants with credit card processing systems affected by a similar form of malicious software.
The news company’s statement didn’t identify the other retailers experiencing the attack — just that the infected systems were at stores with locations in California and New York.
IntelCrawler published another press release to its site on Friday, outlining proof directed to who could end up being the writer of the BlackPOS malware that successfully lifted private data from the magnetic strips on the backs of credit cards belonging to over 70 million Target shoppers between Thanksgiving and December. In accordance with other sources of IntelCrawler the initial infected Point-of-Sales environments by BlackPOS were in Australia, Canada and the US.
Before both breaches IntelCrawler detected large-scale RDP brute-forcing attacks on Point-of-Sales terminals throughout the US, Australia and Canada began at the start of winter, 2013 period attempting weak passwords such as:
"pos":"pos"; "micros":"micros" (MICROS Systems, Inc. - Point-of-Sale Hardware); "edc":"123456" (EDC - Electronic Draft Capture).
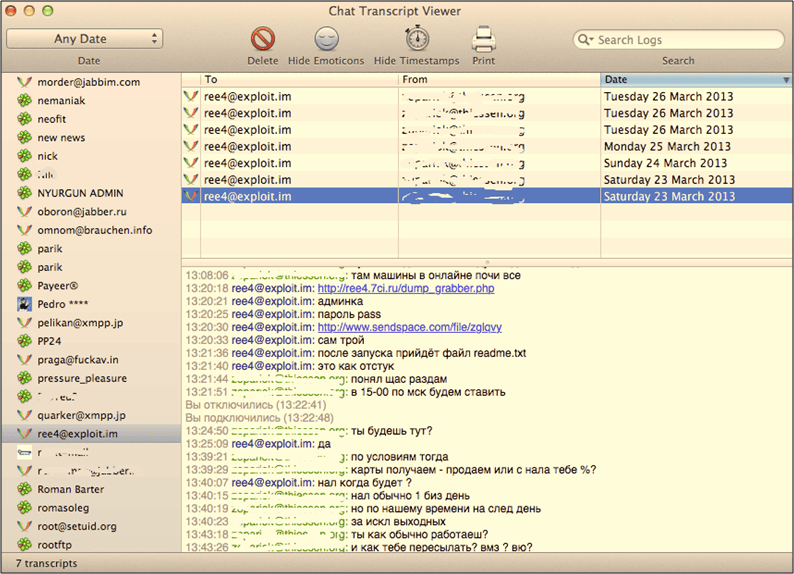
You can view in the above picture the first C&C server of BlackPOS was installed on “ree4.7ci.ru”, which was the personal host of its author “ree“. Some other hosts were found on this domain name, as probably it was used as a hosting for all members of the same group: – onlyddos.7ci.ru; – merzavetz.7ci.ru; – reperckov41.7ci.ru.