The hacker told sources that this zero-day allows him to read and write any file on the forum server without root privileges. He hasn’t provided any other details.
Meanwhile, openSUSE has shut down its forum. The organization’s representatives say they’ve taken this decision because there’s no workaround and no fixes for the exploit. vBulletin has not made any comments on the issue.
So what data has the hacker jeopardized? At first, OpenSUSE mentioned that user accounts couldn’t have been affected because of the authentication system they’re utilizing.
“Credentials for your OpenSUSE login are not saved in our application databases as we use a single-sign-on system (Access Manager from NetIQ) for all our services. This is a completely separate system and it has not been compromised by this crack,” openSUSE said.
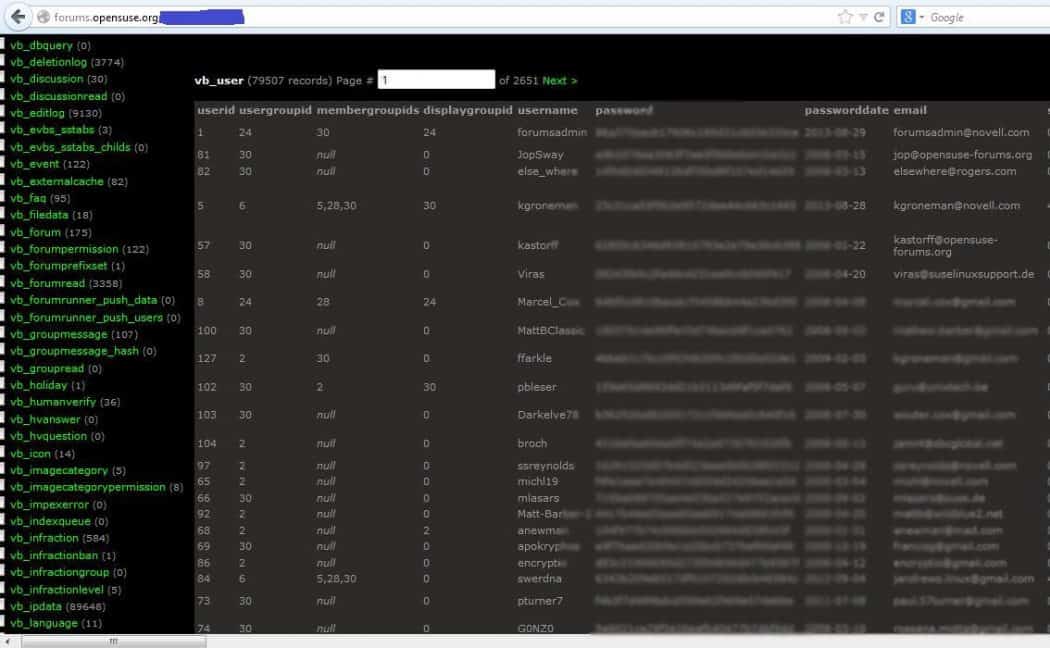
On the other hand, the hacker has provided The Hacker News with an image (see screenshot) which shows that he has gained access to what appears to be encrypted passwords. OpenSUSE says there’s an explanation for that.
The hacker also released pictures of access to the database.
“What the cracker reported as compromised passwords were indeed random, automatically set strings that are in no way connected to your real password,” they noted.
Nonetheless, they acknowledge that the Pakistani hacker has acquired user emails. This isn’t the first time when unconfirmed reports of a vBulletin zero-day surface. In November, hackers of Inject0r Team claimed to have breached MacRumors and the vBulletin.org by exploiting a vBulletin zero-day vulnerability. Inj3ct0r also claims they have a vBulletin zero-day for sale.