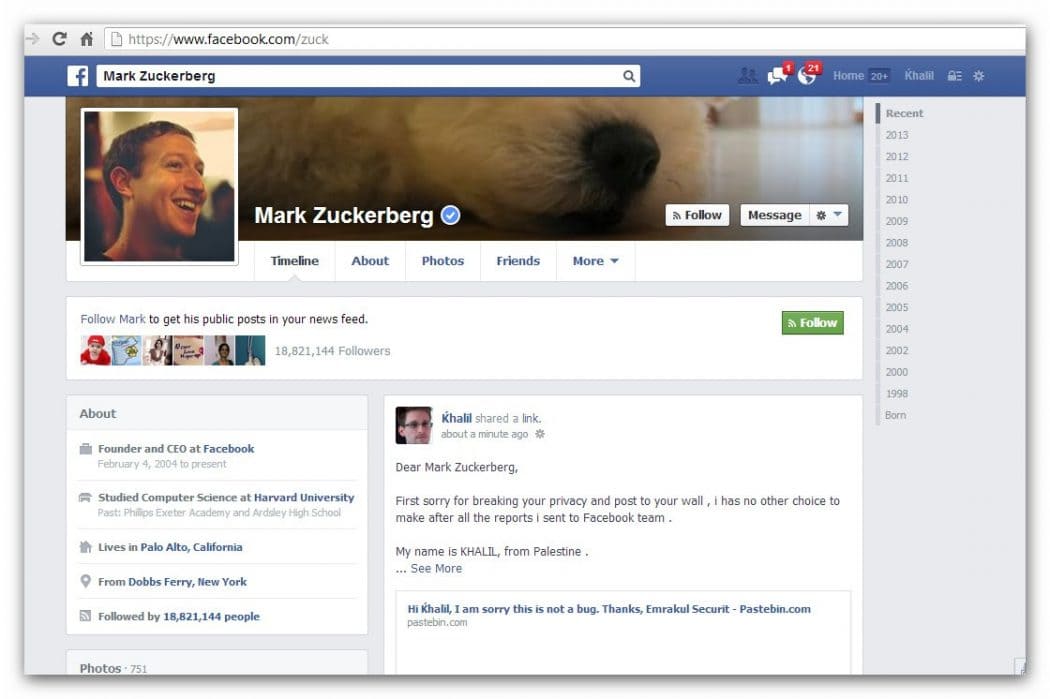
Facebook Exploit “post to Facebook user when they are not on friends list” discovered by Khalil Shreateh states on his blog, that he has discovered this exploit and reported it to Facebook.
Days ago i discovered a serious facebook vulnerability that allows a facebook user to post to all facebook users timeline even they are not in his friend list .
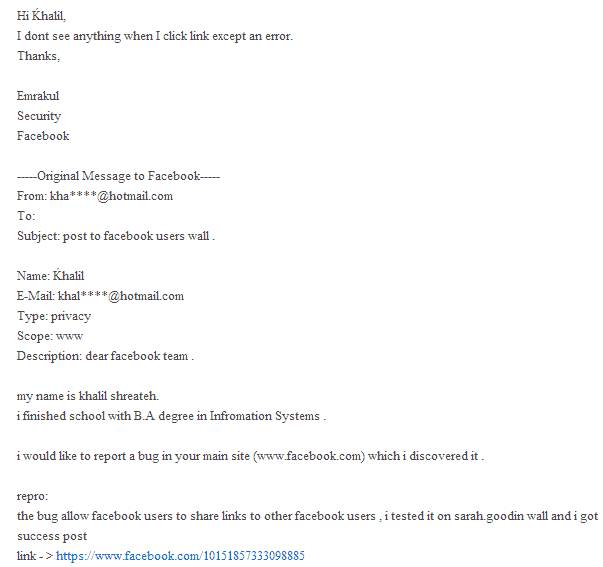
Shreateh reported it via http://www.facebook.com/whitehat and received this message back:
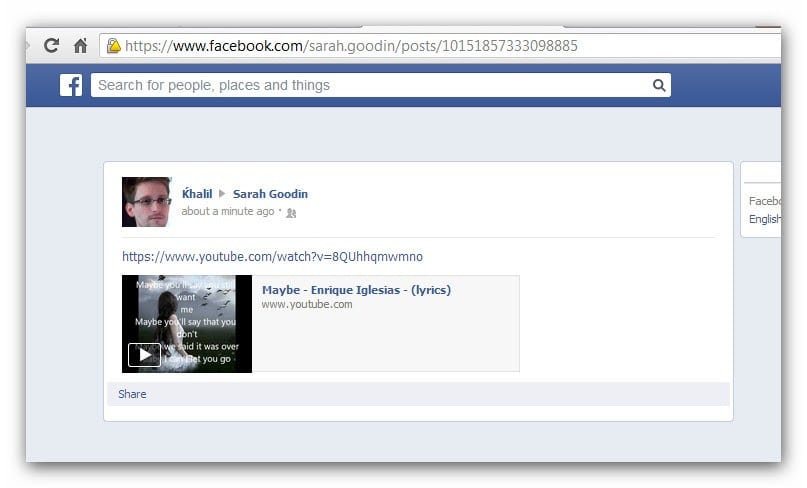
The researcher then demonstratedthe exploit for the Facebook security team which is in denial.
The security team denied all of it stating it was not a exploit, you can read their email below:
a minute after that i got my account disabled ,as they said facebook has all the right to disable any facebook account without any reason given , i made another report asking facebook security to reactivate my account , this is the email shows my report including their replay :
Dear Khalil, Facebook disabled your account as a precaution. When we discovered your activity we did not fully know what was happening. Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it. We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue. When you submit reports in the future, we ask you to please include enough detail to repeat your actions. We are unfortunately not able to pay you for this vulnerability because your actions violated our Terms of Service. We do hope, however, that you continue to work with us to find vulnerabilities in the site. We have now re-enabled your Facebook account. Joshua Security Engineer Facebook -----Original Message to Facebook----- From: [email protected] To: Subject: bypass facebook posts to timeline privacy Name: Khalil Khalil E-Mail: [email protected] Type: privacy Scope: wwwDescription: ok , this is the third time i report this bug , i know that you guys now know that it’s a bug for sure after facebook.com/ola deactivate my account which is facebook.com/khalil.iz.sh i want my account back soon as possible , as i report the bugs for you and i didnt use another fake accounts or test accounts to break privacy . although my account contains important messages that some of my friends need them back . https://fbcdn-sphotos-d-a.akamaihd.net/hphotos-ak-ash3/1174822_10200988067716575_1496625129_n.jpg repro: this the last post i made before " www.facebook.com/ola " deactivate my account , i had no choice after you guys replay twice back again to me that this is not a bug . https://fbcdn-sphotos-d-a.akamaihd.net/hphotos-ak-prn1/543398_10151865722018885_1202186069_n.jpg
The researcher has now released a point of concept (POC) video for the Facebook team.