Malware has been discovered being passed around on Google Play which is very hard to do, but still possible.
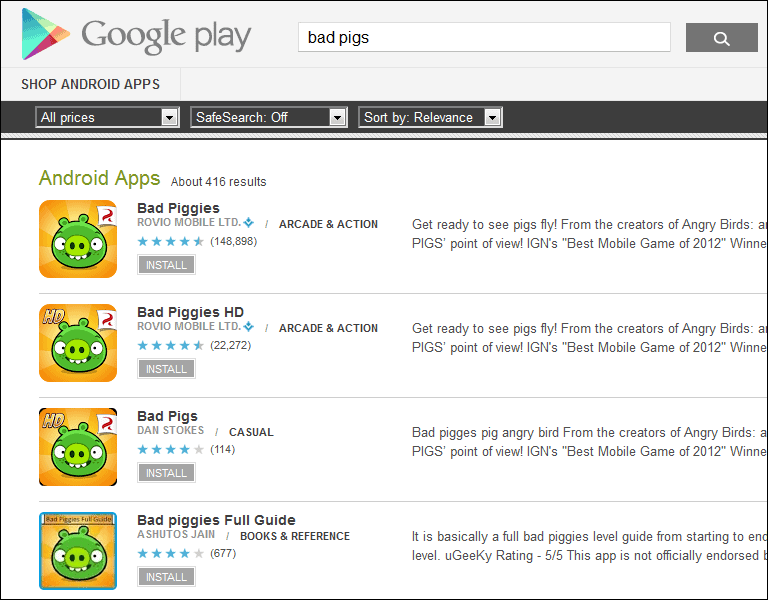
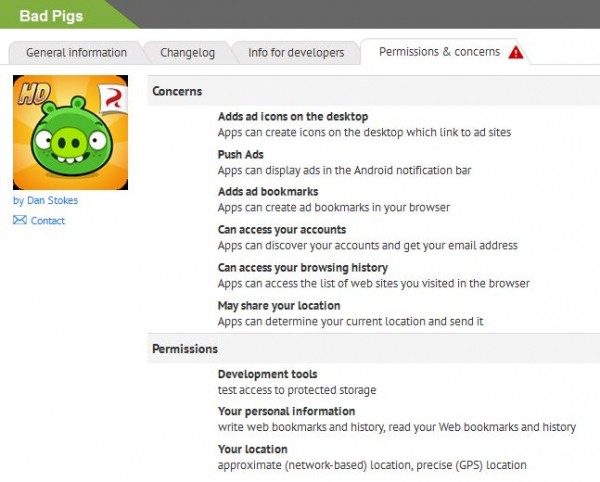
A backdoored version of the “Bad Piggies,” a sequel of the hit game Angry Birds, was spotted on the Google Play store. It was being distributed as “Bad Pigs.”
F-Secure, was the first one to come across the Bad Pig on Google Play and straightaway reported the compromised app to Google.
“These particular piggies aren’t just bad – they’re evil,” F-Secure described the Bad Pigs app in their blog post.
F-Secure has also spotted other apps by the said developer. Other Android apps which malware piggy backing include titles such as “Fruit Chop Ninja” (a ripoff version of Fruit Ninja by Halfbrick Studios) with over 10,000 downloads and “Paper Toss 2” (a ripoff version of Paper Toss 2.0 by Backflip Studios) with more than a thousand downloads.
Android users who have downloaded the Big Pig, Fruit Chop Ninja or Paper Toss 2 must find these apps and erase them. You are able to go to the Android App Manager via the Settings Menu to uninstall the app.
F-Security also stated its mobile security product can discover such malware and remove them as necessary. There are also other tools Android users can use such as Bitdefender Mobile Security and Lookout.