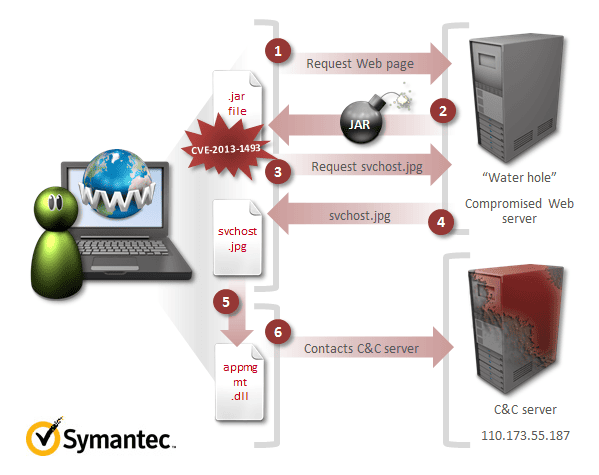
Symantec and released information that they recently received information on a new Java zero-day, Oracle Java Runtime Environment CVE-2013-1493 Remote Code Execution Vulnerability (CVE-2013-1493).
The payload in the attack consisted of a DLL file, detected by Symantec as Trojan.Naid, which connects to a command-and-control (C&C) server IP: 110.173.55.187.
Interestingly, a Trojan.Naid sample was also signed by the compromised Bit9 certificate discussed in the Bit9 security incident update and utilized in an attack on an additional party.
The Trojan.Naid attackers have been extremely persistent and have shown their sophistication in multiple attacks. Their primary motivation has been industrial espionage on a variety of industry sectors. Similar to the targeted attacks by the Stuxnet malware.
Symantec is reported to still be investigating how to protect yourself from this zero-day and is posting updates on their blog.







We’ve put together a online tool to check if Java is enabled in your browser at http://isjavaenabled.com.