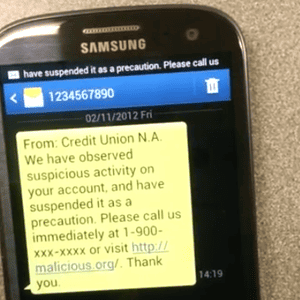
 Android apps are able to trick smartphone users into thinking that they have received a text from an arbitrary sender. These apps can place whatever content they like within these non-texts. This creates the perfect conditions for phishing, or more specifically, SMiShing in this case. A malicious app of this kind could, for example, construct a text claiming to be from PayPal asking the user to enter their access credentials on a fake PayPal web site.
Android apps are able to trick smartphone users into thinking that they have received a text from an arbitrary sender. These apps can place whatever content they like within these non-texts. This creates the perfect conditions for phishing, or more specifically, SMiShing in this case. A malicious app of this kind could, for example, construct a text claiming to be from PayPal asking the user to enter their access credentials on a fake PayPal web site.
The vulnerability was discovered by security researcher Xuxian Jiang’s team at North Carolina State University, which has also been responsible for discovering numerous other Android vulnerabilities. The researcher has posted a YouTube video demonstrating a proof-of-concept app running under Ice Cream Sandwich (4.0.4) and the ancient Donut (1.6). The current Android version, Jelly Bean, is also reported to be vulnerable. According to Jiang, the app does not require any special permissions.
Since the text message never leaves the user’s phone, it does not even require a SIM card. Jiang says that there is no way of detecting that the text is a fake. While Google has confirmed the existence of the problem and promised mitigation, it is unclear when the vulnerability will be fixed or in which versions of Android.
However, Android users should not get their hopes up that the update will suddenly appear on their smartphones as most phone manufacturers are very poor at providing existing customers with operating system updates or security fixes.
Cross-Posted: http://www.h-online.com






