 Security specialist Kaspersky Lab has discovered new versions of the ZeuS trojan apps for Android and BlackBerry devices that are mainly going after mobile TANs (mTANs) for online banking. The attacks primarily target users in Germany, Spain and Italy, where the mTAN system is commonly used by banks to improve security.
Security specialist Kaspersky Lab has discovered new versions of the ZeuS trojan apps for Android and BlackBerry devices that are mainly going after mobile TANs (mTANs) for online banking. The attacks primarily target users in Germany, Spain and Italy, where the mTAN system is commonly used by banks to improve security.
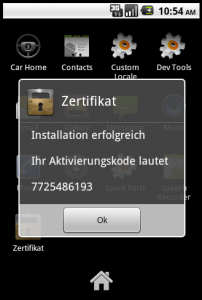
The malware still uses the same basic approach as its predecessors: smartphones are infected via a Windows PC that is infected with the ZeuS trojan. Upon opening an online banking web site on an infected system, the trojan may, for example, inject an alert saying that new certificates must be installed on the smartphone for security reasons. Bogus certificates or security updates are then offered as downloads or, in some cases, are even sent directly to the user’s registered mobile number via an SMS message. Once installed on the device, however, the trojan app secretly forwards the SMS messages that contain the mTANs to another number abroad – current versions send them to two mobile phone numbers in Sweden.
The new trojan samples for Android and BlackBerry devices – Kaspersky Lab calls them “Zeus in the Mobile”, or ZitMo – mainly appear to be used to systematically extend the trojan’s functionality. The Android version’s level of sophistication is still slightly below that of the Windows Mobile, Symbian and BlackBerry versions (an iPhone counterpart has not yet been sighted). For example, it appears to forward not only the bank’s mTAN messages, but all SMS text messages to its command and control centre.
The mTAN system is used by many banks in Germany, several other European countries, and also Russia, South Africa and New Zealand. The system works by generating a TAN on the fly and sending it to the user’s mobile phone when they initiate a transaction. The user then has to enter the TAN to authenticate the transaction.
Source: http://www.h-online.com








#ZeuS #trojan #developed for phones http://t.co/x5uBExyW #Alert
RT @Zer0Security: #ZeuS #trojan #developed for phones http://t.co/x5uBExyW #Alert
RT @Zer0Security: ZeuS #trojan developed for phones – @Zer0Security http://t.co/9BFE3MfB
#app
ZeuS #trojan developed for phones – @Zer0Security http://t.co/9BFE3MfB
#app