SophosLabs reports that it is intercepting a wave of malicious emails that have been spammed out around the world, luring unsuspecting internet users into clicking on a malicious attachment.
The emails all claim to be related to a rejected wire transfer. Although most savvy computer users would realise that unsolicited email is unlikely to be legitimate, there are some who might be vulnerable or merely curious enough to click on the HTML attachment, not realising that it can cause problems for their PC.
Here’s a typical example of an email we have intercepted.

The subject lines used in the malicious spam campaign can vary, but are all related to a “Wire Transfer Confirmation” (some give a reference number in an attempt to make the message appear more official).
Here is a small selection of the subject lines we saw at SophosLabs during the space of just one minute.

Attached to each email is a file called Wire_AMBA01-Rejected.htm, which Sophos products detect as Troj/JSAgent-CK.
To the casual observer, the file may seem harmless enough – displaying a message saying
"Please wait a moment. You will be forwarded...".

But it’s the next section of the HTML code which is interesting. A script deciphers a sequence of numbers into code which the computer then executes.
SophosLabs researchers have tools which help them deobfuscate code like this, to find out what it’s really planning to do..

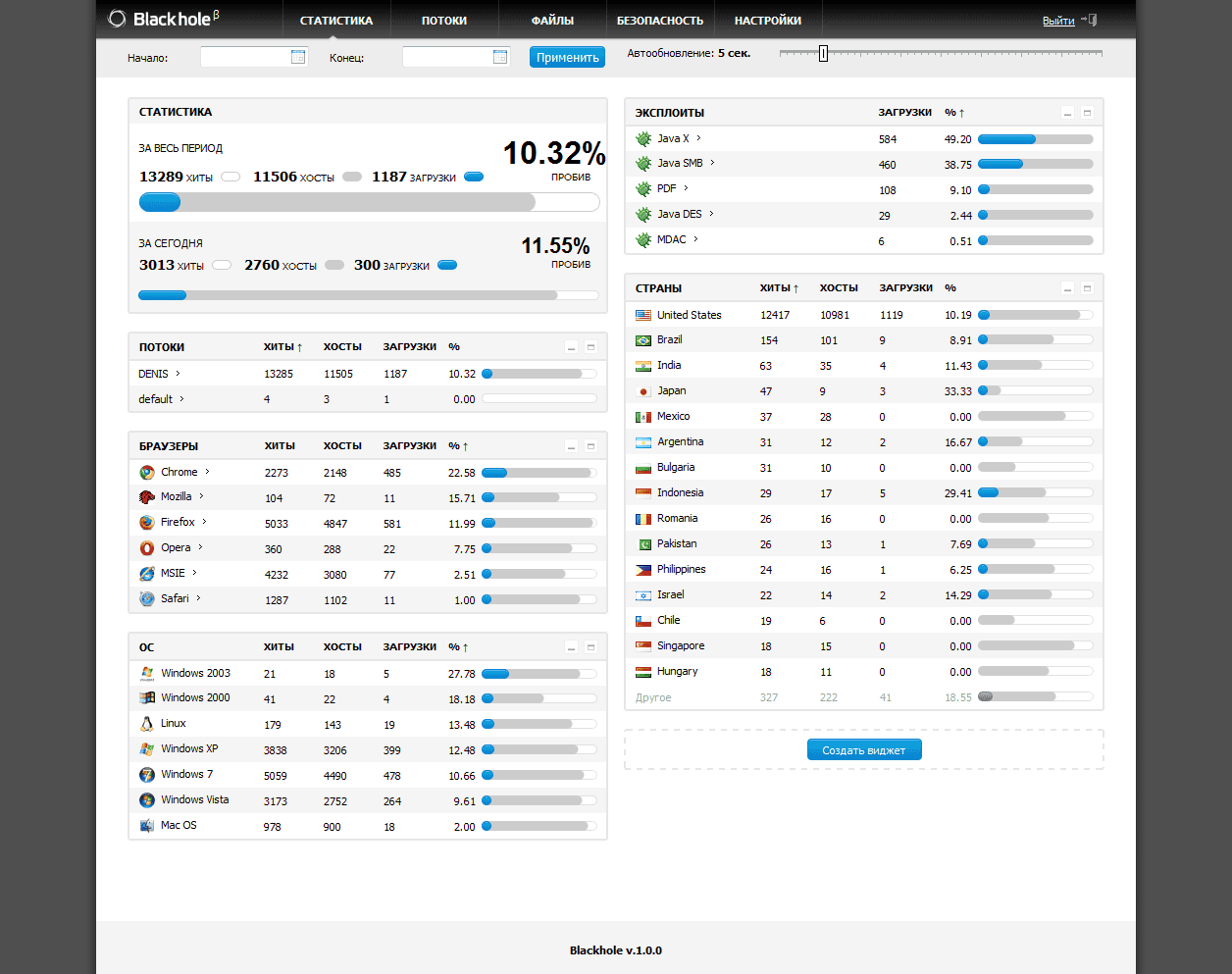
If your computer isn’t properly protected, you will be redirected to a hacked Russian website which is playing host to the Blackhole exploit kit – within seconds your computer will most likely be infected by malware.
– within seconds your computer will most likely be infected by malware.
A few days ago we saw an attack in a similar vein, with a fake Facebook photo tag notification using the Blackhole kit to exploit computers.
As ever, keep your security up-to-date. That not only means running an up-to-date anti-virus, but also ensuring that you have the latest operating system and application patches in place.
Finally, remember to have a spoonful of common sense each morning – and consign unwanted, unsolicited emails to the trash can rather than clicking on any links or attachments that they may contain.







Blackhole Exploit pack poses as rejected wire transfer email http://t.co/FT2JrpJi #Bhole #Malware
Blackhole Exploit pack poses as rejected wire transfer email – @Zer0Security http://t.co/qrtLTa23
RT @Zer0Security: Blackhole Exploit pack poses as rejected wire transfer email – @Zer0Security http://t.co/qrtLTa23