There has been a large scale iframe injection reports indicate. The targets where popular plugins such as TimThumb, a popular api used in WordPress themes to down size images, PHPMyAdmin and Uploadify. The bulk of the sites being targeted are operating Plesk Panel version 10.4.4 or older versions, and investigators from Sucuri have showed that as many as fifty-thousand websites may have been compromised by an unknown botnet operation.
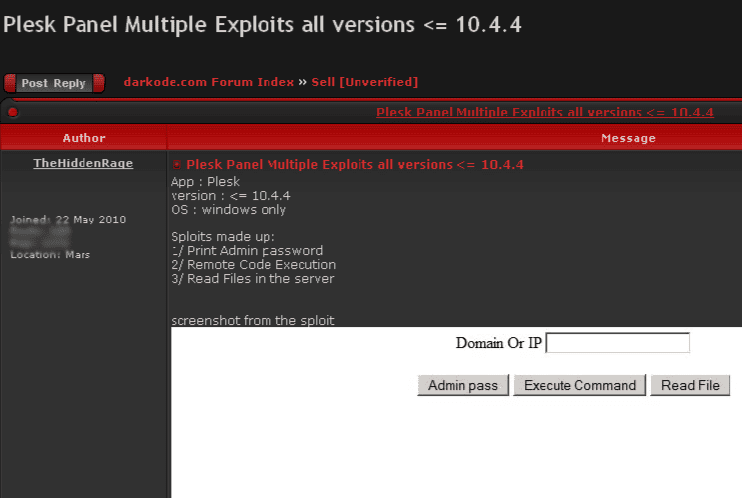
Brian Krebs reports that the assaults are possibly associated to a newly disclosed zero-day exploit for Plesk that’s being sold on the black market for approximately $8,000 per purchase.
Securi’s Daniel Cid seems to say that the vulnerability is a key factor in the swift compromise of the affected websites.
What is interesting is that most of our clients always used to be using CMSs (like WordPress, Joomla, etc), but lately we are seeing such a large number of just plain HTML sites getting compromised and when we look deeper, they are always using Plesk,”
Cid told Krebs.
Last month, malware researcher Denis Sinegubko had provided analysis of the BlackHole Exploit Kit’s successful compromise of several sampled websites, and had determined that a vulnerability in Plesk was probably the culprit.
The bug was afterwards patched, but the recent wave of website hacks are an indication that a different and dangerous flaw in the application may be as of yet unmitigated.
The BlackHole Exploit Kit is among the most popular exploit packs in the underground market, and Symantec’s analysis of the most recent incarnation exposed it was altered to make use of an unpatched vulnerability in Microsoft XML Core Services (CVE-2012-1889) to facilitate drive-by attacks on Internet users.