A complex directed cyber-attack that gathered private information from nations such as Israel and Iran has been exposed, researchers have enounced.
Kaspersky Laboratories said to BBC they believed the malware, called Flame, had been functioning since August  2010. The complexity and functionality of the recently discovered malicious program outmatch those of all other cyber threats known to date. This new threat is more sophisticated than Duqu and Stuxnet. This is just an example of how sophisticated cyber threats are out there and haven’t been discovered yet.
2010. The complexity and functionality of the recently discovered malicious program outmatch those of all other cyber threats known to date. This new threat is more sophisticated than Duqu and Stuxnet. This is just an example of how sophisticated cyber threats are out there and haven’t been discovered yet.
The ‘Flame’ cyber espionage worm came to the attention of our experts at Kaspersky Lab after the UN’s International Telecommunication Union came to us for help in finding an unknown piece of malware which was deleting sensitive information across the Middle East. While searching for that code – nicknamed Wiper – we discovered a new malware codenamed Worm.Win32.Flame.
Flame is similar and shares many characteristics with the notorious malware threats, Duqu and Stuxnet. It’s features are different, but geography and careful targeted attacks coupled with the usage of software vulnerabilities are similar to what Duqu and Stuxnet used.
The current techniques that Flame uses to infect its targets:

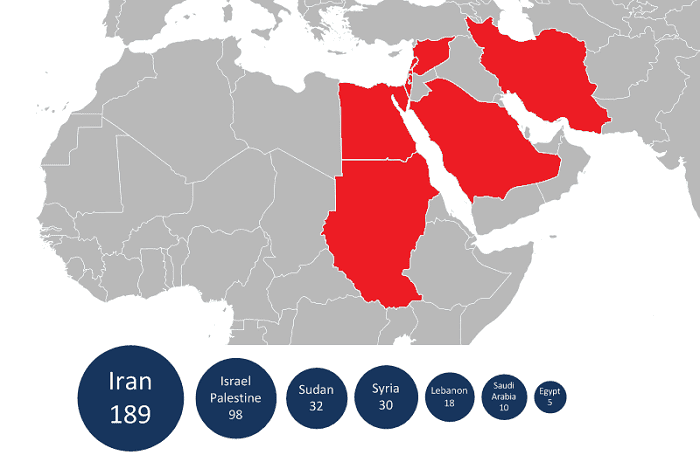
The malware seems to be targeting and infecting Middle East countries:
Kaspersky notes:
Although we are still analyzing the different modules, Flame appears to be able to record audio via the microphone, if one is present. It stores recorded audio in compressed format, which it does through the use of a public-source library.
Recorded data is sent to the C&C through a covert SSL channel, on a regular schedule. We are still analyzing this; more information will be available on our website soon.
The malware has the ability to regularly take screenshots; what’s more, it takes screenshots when certain “interesting” applications are run, for instance, IM’s. Screenshots are stored in compressed format and are regularly sent to the C&C server – just like the audio recordings.
We are still analyzing this component and will post more information when it becomes available.
Story will be updated as we get more information
For Kaspersky’s complete analysis: http://www.securelist.com/en/blog/208193522/The_Flame_Questions_and_Answers






Comments 1