 The Waledac botnet brought offline in February 2010 is all the same very much dead, but the code used to produce the spamming botnet has been revised and recoded for a darker purpose: stealing passwords.
The Waledac botnet brought offline in February 2010 is all the same very much dead, but the code used to produce the spamming botnet has been revised and recoded for a darker purpose: stealing passwords.
Security firm, Palo Alto Networks has detected a new strain of Waledec malware, targeting users February 2nd. This time the strain is doing more then just sending spam mail. The newer version has been recoded to include stealing of passwords, and authentication data, also known as form grabbing. This abilities include decoding saved FTP, POP3, SMTP credentials and also steals .dat files for FTP and Bitcoin. All this information is uploaded to the botnets C&C Palo Alto Networks claims.
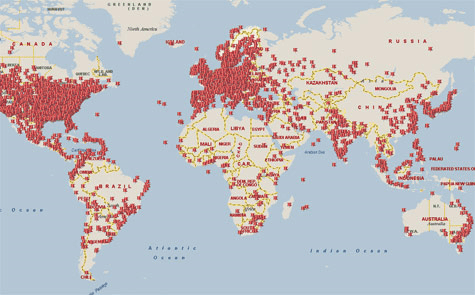
The pervious versions infection status, which was brought down by Microsoft two years ago:
The MD5 for this sample is 0766243f2520c32f1f6b4661c0b5592e, and customers can login to the WildFire Portal to see the analysis if this malware was detected on their network. Palo Alto Networks customers who are running PAN-OS version 4.1 are strongly encouraged to enable WildFire if they have not already done so in order to gain protection from similar threats in the future. (Note: All Palo Alto Networks customers with a valid Threat Prevention license are already protected if they have applied the latest AV updates). WildFire is a free feature, and users benefit from protections from threats seen by all Palo Alto Networks customers worldwide.
To avoid confusion, it is important to note that this is a new variant of the botnet, and not the original version, which remains under the control of Microsoft.







Unquestionably believe that which you setatd. Your favorite reason seemed to be on the internet the simplest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they just don’t know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people could take a signal. Will probably be back to get more. Thanks!