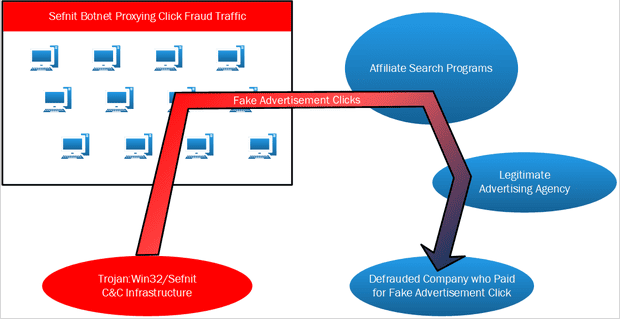
Microsoft’s Malware researcher Geoff McDonald verifies that malware dubbed the Sefnit is driving a monumental click fraud operation and is the same family of malware as the recently discovered Mevade botnet thought responsible for a spike in Tor network connections.
In June of 2013 the researchers revealed a click fraud component which they first classified as Mevade, the malware credited with being responsible for a 600% growth in the Tor network which was first believed to be a blowback from the NSA leaks.
“Last week we concluded, after further review, that Mevade and Sefnit are the same family and our detections for Mevade have now been moved to join the Sefnit family,” McDonald stated.
“The new Sefnit click fraud method is a departure from the method previously used back in 2011. This new, stealthier methodology is believed to be largely responsible for Sefnit being able to evade AV vendor detection during the last couple of years,” he added.
Who’s behind it? Trend Micro‘s TrendLabs ties Mevade to a specific criminal gang operating out of Ukraine and Israel.
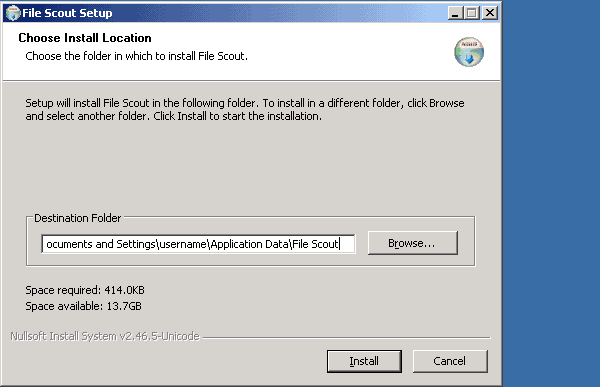
How does it infect systems? It seems to hide inside other programs. TrendLabs says they have seen adware downloaded through the Mevade botnet. Microsoft says they have seen it silently install as part of an application called “File Scout”, and there are strong indications that the same programmer(s) wrote Meade/Sefnit and File Scout.